What Are Verifiable Credentials and How Do They Work on the Blockchain?
Learn how verifiable credentials use blockchain infrastructure to embed cryptographic proof into digital documents, shifting trust from institutions to data.
Niels van den Bergh
CEO
April 16, 2026
Understanding Verifiable Credentials
Verifiable credentials are digital documents with authenticity baked in mathematically. Unlike traditional digital certificates that require external validation, these credentials carry cryptographic proof of who issued them and whether anything has been changed since.
Think of a digital diploma that vouches for itself. It holds the core details, including degree type, graduation date, and student name, alongside cryptographic signatures that confirm the institution issued it and that nothing has been touched since.
The Three-Party Model
Verifiable credentials work within a three-party ecosystem:
Issuers create and digitally sign credentials. Universities issue diplomas, governments issue licences, employers issue certifications. The issuer's digital signature provides cryptographic proof of authenticity.
Holders receive and store their credentials. Graduates store diplomas, professionals maintain licences, employees keep certifications. Holders decide when and how to share their credentials.
Verifiers check credential authenticity when presented. Employers verify job applicants' qualifications, regulatory bodies check professional licences, service providers confirm user eligibility.
The W3C Verifiable Credentials Standard
The World Wide Web Consortium (W3C) created the verifiable credentials specification to ensure interoperability across different systems and platforms. This standard defines how credentials should be structured, issued, and verified regardless of underlying technology.
Core Components of W3C Verifiable Credentials
Credential Metadata covers information about the credential itself: issuer, creation date, expiration, and credential type.
Claims hold the actual information being asserted. A driver's licence might include the holder's name, address, licence class, and restrictions.
Proofs deliver cryptographic evidence that the credential is authentic and unaltered. These mathematical signatures let anyone verify credential integrity without contacting the original issuer.
Schemas define structure and format for different credential types, ensuring consistency across issuers and enabling automated processing.
The W3C standard creates a common language. Credentials issued by one system are compatible with completely different verification platforms. This cross-platform interoperability is what makes widespread adoption possible.
How Blockchain Enables Verifiable Credentials
Verifiable credentials can function without blockchain, but distributed ledger technology solves critical challenges in enterprise-scale credential management.
Decentralised Identifier Resolution
Blockchain networks host decentralised identifiers (DIDs) that let verifiers look up an issuer's current public keys without relying on central authorities. When a university issues a diploma, its blockchain DID points to the cryptographic keys used to sign that credential.
When universities rotate signing keys for security, they update their DID document on the blockchain. Verifiers automatically use current keys when checking credentials, even those issued years earlier with different keys.
Immutable Audit Trails
Every credential lifecycle event, including issuance, revocation, and updates, gets written to the distributed ledger permanently. That record can't be quietly edited or erased after the fact, which matters enormously when you need to prove what happened and when. This immutable audit trail is the foundation of trustworthy credential management.
For regulatory compliance, this is particularly valuable. Organisations can point to a clear, timestamped history showing which credentials were valid at any given moment and that their verification processes held up to scrutiny.
Revocation Without Central Dependencies
Traditional credential systems hit a wall with revocation. When a professional licence gets suspended, verifiers face a dilemma: check with the issuing authority every single time, or risk accepting invalid credentials.
Blockchain-based revocation registries cut through this problem. Issuers update the distributed ledger registry when they revoke credentials. Verifiers query the ledger directly, no need to chase down the original issuer.
Why Blockchain Architecture Matters for Credential Privacy
Not all blockchains handle credential privacy the same way. The difference comes down to how the ledger structures transactions. Account-based models like Ethereum (EVM) tie every transaction to a single visible account address. If a verifier knows that address, they can see every credential event associated with it. One verification check exposes the holder's entire credential history.
UTXO-based ledgers (Unspent Transaction Output) work differently. Each credential transaction is a separate, independent output with no structural link to the holder's other credentials. A verifier checking one credential learns nothing about what other credentials the holder has, when they were issued, or who issued them. The ledger itself is public and auditable, but individual credential histories remain isolated from each other. mintBlue's infrastructure uses this UTXO architecture specifically because credential systems demand this kind of privacy. The result is a system that is publicly transparent for auditability, yet completely private at the individual credential level.
Real-World Applications
Verifiable credentials on blockchain already solve practical problems across industries.
Professional Licensing
Medical boards issue digital licences as verifiable credentials. Hospitals skip the wait for manual confirmation from licensing authorities and verify a doctor's credentials in seconds. Licence suspensions or restrictions appear in the distributed ledger registry immediately.
Educational Credentials
Universities issue diplomas and transcripts as verifiable credentials. Employers verify qualifications instantly, while students control exactly what they share, whether that is specific courses, grades, or just the degree, based on what each application requires. The cryptographic proof makes academic fraud nearly impossible.
Supply Chain Verification
Manufacturers create certificates of origin, quality testing results, and compliance documentation as verifiable credentials. Each product batch carries cryptographically signed records of its journey and testing history. Buyers verify authenticity without needing direct access to the manufacturer's internal systems. mintBlue already provides the data anchoring infrastructure for supply chain clients to issue and verify these credentials at scale, handling the cryptographic complexity so manufacturers focus on their products rather than building distributed ledger capabilities from scratch.
Identity Proofing
Financial institutions and service providers streamline customer onboarding with verifiable credentials. Rather than collecting and storing copies of identity documents, they verify credentials cryptographically and record only the verification result. Storing less data shrinks attack surfaces and simplifies compliance. In the Netherlands, mintBlue works with government bodies including the Belastingdienst on document verification infrastructure that anchors credential proofs to a distributed ledger, giving both citizens and agencies a tamper-proof verification trail.
From Cryptographic Proof to Legal Standing
A verifiable credential can prove that data hasn't been tampered with. But in regulated industries, cryptographic integrity alone is not enough. The credential also needs to prove that the issuer is a legally verified entity and that the signature holds up in court.
This is where Self-Sovereign Identity (SSI) frameworks and eIDAS-qualified digital signatures come in. When a credential is issued with an eIDAS-compliant signature, it carries the same legal weight as a handwritten signature across all EU member states. The credential doesn't just confirm "this was issued." It confirms "this was issued by a verified legal entity, with a signature that satisfies EU regulatory standards." mintBlue's infrastructure embeds eIDAS-compliant identity into every credential transaction, bridging the gap between cryptographic proof and legal validity. For organisations operating across EU borders, this removes the question of whether a digitally signed credential will be recognised by regulators, courts, or counterparties in another member state.
Technical Implementation
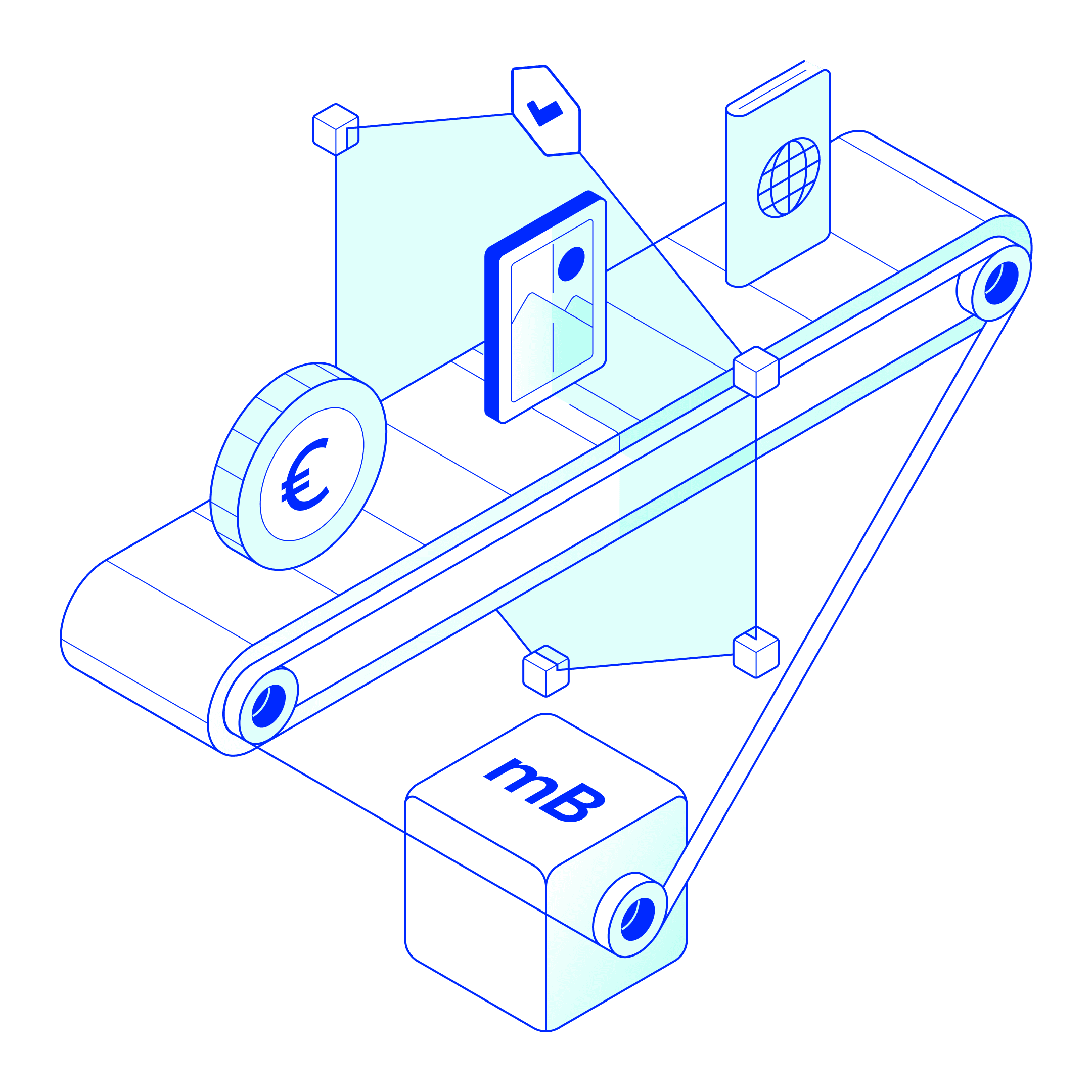
Implementing verifiable credentials on a distributed ledger requires several technical components working together. mintBlue's infrastructure handles the cryptographic complexity of credential issuance and verification, so organisations focus on their verification workflows rather than building blockchain capabilities from scratch.
Credential Issuance
Issuers generate credentials by creating structured JSON documents containing claims about the subject. To sign them, they use cryptographic keys tied to their blockchain-based DID. What comes out the other end is a credential that bundles the original claims together with cryptographic proof, self-contained and independently verifiable.
Secure Storage
Holders keep credentials in digital wallets designed to protect cryptographic proofs while still supporting selective disclosure. More sophisticated implementations layer in zero-knowledge proofs, so holders can share a specific claim, such as age verification, without exposing the rest of the credential.
Verification Process
Verifiers receive presented credentials and perform several checks: validating cryptographic signatures, confirming issuer identity through their blockchain DID, checking revocation status against blockchain registries, and ensuring credentials haven't expired.
Privacy Protection
Current implementations support selective disclosure, letting holders share only necessary information. Someone proving they're over 21 shares age verification without revealing exact birthdate, address, or other personal details.
The strongest privacy guarantees come from source-retained architecture, where the credential holder's personal data never leaves their own wallet or system. The blockchain stores only cryptographic proofs, not the underlying data. Verification works by comparing these proofs against what the holder presents, not by pulling raw data through a centralised platform. This matters because many credential verification services route all credential data through their own servers, creating a central point where personal information accumulates and can be breached or misused. In a source-retained model, even the infrastructure provider has zero access to credential contents. mintBlue's architecture follows this principle. It acts as the postal service, moving sealed envelopes between parties without ever opening them. The cryptographic proofs on the ledger let verifiers confirm authenticity, while the actual credential data stays with the holder.
Benefits for Organisations
Organisations implementing verifiable credentials gain several operational advantages.
Reduced Verification Costs: Manual document checking eats up time and money. Cryptographic verification runs automatically, eliminating staff hours spent chasing confirmations and fees paid to third-party verification services.
Improved Security: Credentials with valid cryptographic proof resist forgery attempts. Organisations can trust what they've verified instead of second-guessing whether documents have been altered or fabricated.
Regulatory Compliance: The distributed ledger audit trail does more than support security. It produces concrete, timestamped evidence that verification processes were actually followed. When regulators come asking, the record is already there.
Streamlined Operations: Faster onboarding, less paperwork, fewer manual handoffs. Automated verification removes the friction from any process that depends on credential checks.
Challenges and Considerations
Despite their advantages, verifiable credentials face several implementation challenges.
Technical Complexity
Building verifiable credentials right requires expertise across cryptography, distributed ledger infrastructure, and identity management. These are three specialised fields that don't often overlap. Organisations lacking this expertise internally need technology partners with proven track records, not just vendors promising easy solutions.
Standardisation Gaps
The W3C specification provides solid groundwork, but platforms implement details differently, creating compatibility headaches. Organisations must evaluate compatibility upfront or plan for integration work when connecting different systems.
User Experience
Credential holders need digital wallets and enough understanding to manage their credentials effectively. Consumer adoption will lag until this experience becomes straightforward and intuitive.
Legal Recognition
Digital credential regulations are still developing in most jurisdictions. Organisations need to stay on top of local legal requirements while building systems flexible enough to adapt as those rules evolve. With eIDAS-compliant digital signatures, verifiable credentials become legally binding across all EU member states, giving organisations a clear regulatory foundation to build on.
The Future of Verifiable Credentials
Verifiable credentials move identity verification from institutional custody to individual control. As blockchain infrastructure matures and implementation standards align, this approach could become the standard for credential verification across industries.
The economics already make sense, with reduced verification overhead and stronger fraud resistance. Privacy-preserving techniques like zero-knowledge proofs make the proposition even more attractive. Organisations streamline their processes while individuals gain real control over their data.
For teams just getting started, focus on areas where verification costs sting most or fraud risk runs highest. Starting in a controlled environment, such as internal credentials or trusted partner networks, builds expertise before expanding to broader applications.
mintBlue provides the distributed ledger infrastructure that enterprises and governments use to issue, anchor, and verify credentials at scale. Rather than building blockchain capabilities in-house, organisations connect to mintBlue's API and start issuing verifiable credentials within days.