Share fraud signals across organisations. Without sharing the data behind them.
Dutch government agencies use mintBlue to verify identities, share fraud signals, and produce court-admissible evidence under the EU eIDAS framework. Data stays at the source. Verification happens in seconds.

Piloted and deployed with Dutch government agencies for fraud detection and identity verification
mintBlue turned our nightmare of invoice exchanges into a dream of automation. Now we strive to make taxation less of a headache for everyone involved.
Claire Arens
Innovation & Strategy, Netherlands Tax Administration
6 million invoices annually validated and processed automatically. No manual reconciliation. No disputes over what was agreed.
Sebastian Toet
Solutions Architect, VISMA | Yuki
Real-time, verifiable carbon tracking across our entire supply chain without exposing sensitive supplier data.
Pauline Van Ostaeyen
Cofounder, Dockflow
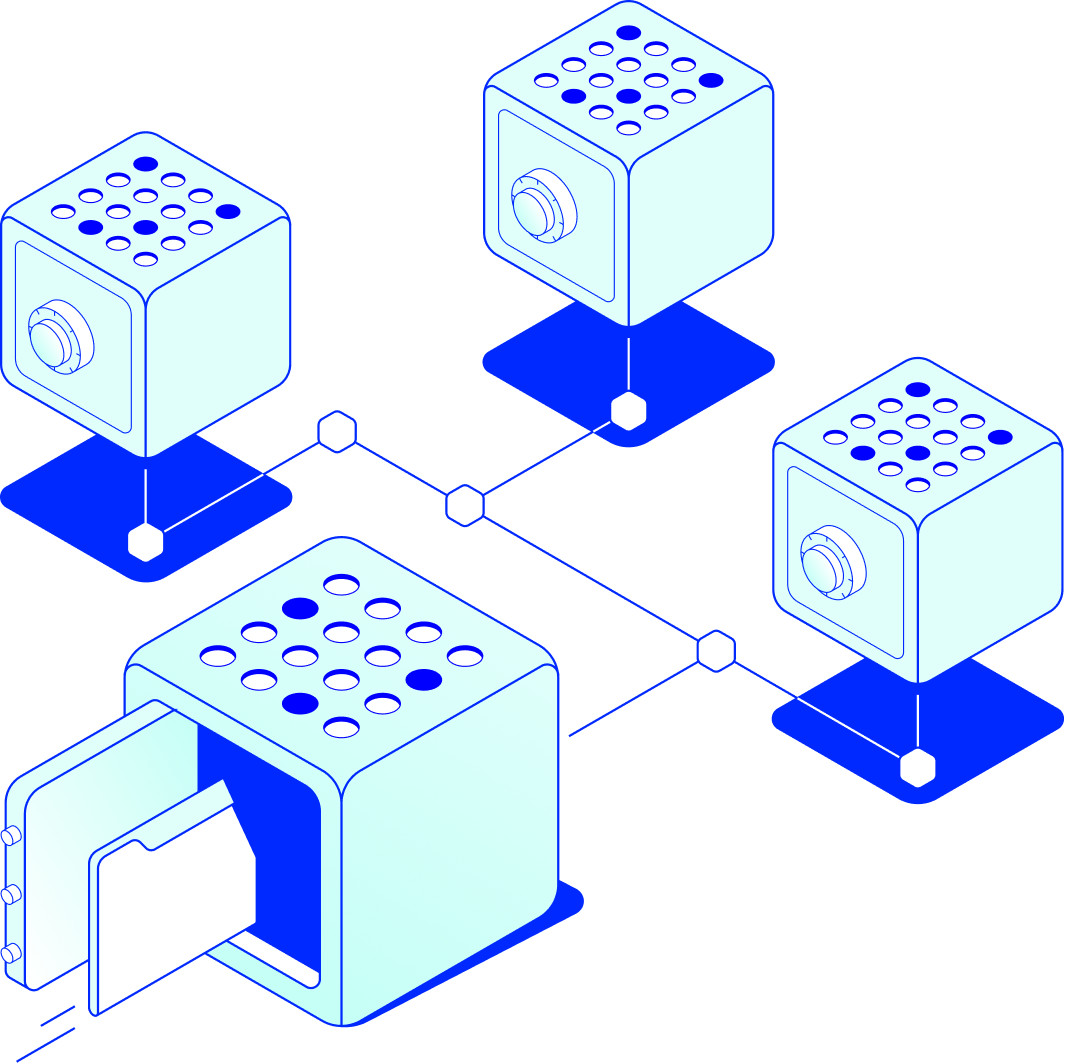
Three verification problems. One infrastructure.
Identity fraud, cross-authority intelligence, and document integrity all require the same foundation: cryptographic proof of what happened, when, and by whom.
HOW IT WORKS
From raw data to verified intelligence in four steps
Data stays where it is. Verification happens across organisations without centralisation.
- 01
Data stays where it is
Each participating organisation keeps full control of its own data. No central database. No data lake. Records remain in the systems they already use.
- 02

Records are hashed and sealed
Relevant data points are converted to cryptographic hashes at each organisation. The original data never leaves. Only the hashes, which cannot be reversed into the original information, are used for matching.
- 03
Hashes are matched across authorities
Hashes from different organisations are compared automatically. When matches exceed a predefined threshold set by the participating authorities, the system flags a potential pattern. No human sees raw data from another organisation during this step.
- 04
Targeted data is shared with proof
Only when the threshold is met, specific data is decrypted and shared with the relevant parties. Every disclosure is logged with a cryptographic audit trail: who accessed what, when, and under which legal basis. The entire chain is court-admissible.
Why governments are moving away from centralised platforms and manual processes
Manual processes offer strong privacy by default but zero cross-organisational intelligence. Centralised surveillance platforms offer full visibility but require every participant to hand over data custody to a single vendor. Neither approach gives you verification without centralisation.
Distributed verification changes the equation.
Manual Processes & Centralised Platforms
- Fraud pattern detection limited to what one authority can see in its own data
- Privacy protection either too high (preventing legitimate sharing) or too low (vendor sees everything)
- Legal admissibility disputed. Evidence trails are incomplete and often contested.
- Does not scale. More authorities means more bilateral agreements and more overhead.
mintBlue
- Cross-authority matching via blind hashing. Patterns detected without exposing raw data.
- Privacy built in. Data is never exposed until a verified threshold is exceeded. GDPR-compliant.
- Court-admissible across the EU under eIDAS. Cryptographic seals on every record.
- Scales with participating organisations and data volume. No per-seat licensing.

GET STARTED
Fraud detection that respects the boundaries it crosses
A 30-minute technical briefing will show you how blind hash matching, cryptographic seals, and threshold-based disclosure work in practice. No sales pitch. Bring your architects.
GET STARTED
Fraud detection that respects the boundaries it crosses
A 30-minute technical briefing will show you how blind hash matching, cryptographic seals, and threshold-based disclosure work in practice. No sales pitch. Bring your architects.
